-
Posts
968 -
Joined
-
Last visited
-
Days Won
7
Content Type
Profiles
Pages
Forums
Downloads
Posts posted by SeedTheNet
-
-
11 hours ago, New_Style_xd said:
Have you ever heard about the DISM++ tool? It does a very good job of cleaning your computer.
I bet this is a GUI for the command DISM
https://learn.microsoft.com/en-us/windows-hardware/manufacture/desktop/what-is-dism?view=windows-11
I will take a look at it , thanks for suggestion brother.

-
20 hours ago, New_Style_xd said:
I can't send you a private message, I'm going to ask you a question, you can answer it right here.
Can you post a serial of any program here on the forum?
I will see why you cannot PM me , but no it is against the site rules to provide keys.
-
On 9/29/2023 at 6:53 PM, New_Style_xd said:
Link Removed
Before in the days of Windows XP , this used to be more helpful because before the CPUs were slow and not that much big disk space and by the time Windows will grow slow , those apps used to come in play
But in those days , I don't find them useful , if you are on Windows 10+ , don't use those as a personal opinion , waste of time and Windows does that job for itself.
-
On 5/10/2023 at 12:57 AM, New_Style_xd said:
Good to know about that my friend.

DrWeb has posted an article about Remcos
-
Sometimes after updating Ubuntu or some accident happen and you manage to get yourself disconnected or restarted the wrong service after the update
Connecting back again would show you this error message :

Normally restarting the server would allow us to connect again , but if a restart isn't possible we will have to SSH to the machine so we can get back to XRDP
After logging into SSH , we have to run this command
https://manpages.ubuntu.com/manpages/jammy/man1/loginctl.1.html
loginctl — Control the systemd login manager
sudo loginctl list-sessionsYou will receive output like this
SESSION UID USER SEAT TTY 246 1000 TESTUSER pts/0 c2 1000 TESTUSER seat0
Your XRDP sessions would be most likely as c1 , c2 , c3 ,c4 etc...
We will run after
sudo loginctl terminate-session <your session ID> sudo loginctl terminate-session c2
After terminating the session it would be possible again to login in XRDP.
-
In this topic we will explain on how to remove Trojan/Remcos from your PC.
Remcos is a RAT type malware that attackers use to perform actions on infected machines remotely. This malware is extremely actively caped up to date with updates coming out almost every single month.
We will have to use an Antivirus to clean up the stuff for us , for example : ESET , Kaspersky , Fortinet or any other good vendor, but those are our recommended vendors.
Before around a month(from this topic date) , Remcos weren't known to most AV vendors and the file can be seen here :
A full analysis : https://any.run/report/b1afbce51ad052f936b989214964d56e2290a7fb5548763273c1fc4382cd5c1c/f26fd95b-3cc1-4578-abf1-17289380ebe5
------------------------------
Regenererede.vbs - https://www.virustotal.com/gui/file/08739fea7bfdf3b641709a3d5b6e6d64be4ea75375dda9fe5cf7234e40cfbe12/detectionTrueCrypt.exe - https://www.virustotal.com/gui/file/b1afbce51ad052f936b989214964d56e2290a7fb5548763273c1fc4382cd5c1c/detection
And then the Trojan proceeds to drop multiple files including a legit and trusted but vulnerable executables
Python.exe
VLC.exe
notepad++.exe
Firefox.exe
Yet the .dll with those files are the ones that are infected/hijacked , and those are the files that will be included with those vulnerable executables
ss3.dll - https://www.virustotal.com/gui/file/65327e1555994dacee595d5da9c9b98967d1ea91ccb20e8ae4195cd0372e05a0
And so on to prevent the Trojan from coming back again , we have to check the Task Scheduler in Windows
There would be weird entries with very long commands for the fake executables that we explained about, upon entering the Task Scheduler incase you find any of these vulnerable executables are set to run everyday, make sure to remove the entries, and also as far as we know that in Windows 10, the Trojan is able to create a startup entry also, that can be taken out through
Examples of Task Scheduler entries that we must remove
<Command>C:\Users\xxxxxxx\AppData\Roaming\Adobe\python.exe</Command> <Arguments>--yoky=66585 --uapb --vgb --mgxfde</Arguments> <Command>C:\Users\xxxxxxx\AppData\Roaming\36c011cd\vlc.exe</Command> <Arguments>-cbriqvr</Arguments>
Downloading Autoruns from Microsoft https://learn.microsoft.com/en-us/sysinternals/downloads/autoruns , and then using Autoruns to see what runs on Logon, a weird entry should be there for one of the fake executables or something to run Powershell , we also need to remove it
Yet there are few images that are downloaded from imgur.com which they contain the load as Steganography which is the code is hidden inside a photo so it can avoid detections, and then it will be decrypted through somekind of application inside the computer probably the vulnerable ones that are provided with the trojan.

Photo source : BleepingComputer
Those are marked as CLEAN in VT because they are encrypted, but Fortinet also checked them and detects them , but in VT still shows clean.
<Regenererede.vbs> with MD5: e627f016283c17b4badc6f5b47f677d3 - <VBS/Agent.77d3!tr> <SciLexer.dll> with MD5: 688c0480ed192ed336911d7ed3730561 - <W32/Rugmi.0561!tr> <Fruit.png> with MD5: c2a09a3c72717c71a6ac22c9f342a0d2 - <Data/Agent.STGP!tr> <ms.png> with MD5: 7b2f3421621a080c2043e6c90821c618 - <Data/Agent.STGP!tr> <Fruit.png> with MD5: fd5cb5160053fcd028ad81016357dff5 - <Data/Agent.STGP!tr> <Pine.png> with MD5: 7f5546e1202e06e17c3eabe86107a504 - <Data/Agent.STGP!tr> <Fruit.png> with MD5: 0086f1ed58e6516027bdc7d8a6c2c9ad - <Data/Agent.STGP!tr>
Any of those files if they are available somewhere in your AppData Roaming folder , then you should remove them manually if an AntiVirus doesn't pick them up.
If more assistance is needed about this Trojan , please reply to this topic.
-
Whatsapp has moved installer to Microsoft Store only
If you cannot use Microsoft Store in your environment , you can use this direct download link from Whatsapp website
https://web.whatsapp.com/desktop/windows/release/x64/WhatsAppSetup.exe
Currently this version shows [OUTDATED] and a black Whatsapp icon.
-
 1
1
-
-
https://www.fortiguard.com/psirt/FG-IR-22-401
Summary
A relative path traversal vulnerability [CWE-23] in FortiOS and FortiProxy may allow privileged VDOM administrators to escalate their privileges to super admin of the box via crafted CLI requests.
Affected Products
FortiOS version 7.2.0 through 7.2.3
FortiOS version 7.0.0 through 7.0.8
FortiOS version 6.4.0 through 6.4.11
FortiOS version 6.2.0 through 6.2.12FortiProxy version 7.2.0 through 7.2.1
FortiProxy version 7.0.0 through 7.0.7
FortiProxy version 2.0.0 through 2.0.11
FortiProxy 1.2 all versions
FortiProxy 1.1 all versionsNote: Impact on FortiProxy 7.0.x, 2.0.x, 1.2.x, 1.1.x is minor as it does not have VDOMs
Solutions
Please upgrade to FortiProxy version 7.2.2 or above
Please upgrade to FortiProxy version 7.0.8 or above
Please upgrade to FortiProxy version 2.0.12 or above
Please upgrade to FortiOS version 7.2.4 or above
Please upgrade to FortiOS version 7.0.9 or above
Please upgrade to FortiOS version 6.4.12 or above
Please upgrade to FortiOS version 6.2.13 or aboveAcknowledgement
Internally discovered and reported by Théo Leleu of Fortinet Product Security team. -
https://www.fortiguard.com/psirt/FG-IR-23-001
Summary
A buffer underwrite ('buffer underflow') vulnerability in FortiOS & FortiProxy administrative interface may allow a remote unauthenticated attacker to execute arbitrary code on the device and/or perform a DoS on the GUI, via specifically crafted requests.
Exploitation status:
Fortinet is not aware of any instance where this vulnerability was exploited in the wild. We continuously review and test the security of our products, and this vulnerability was internally discovered within that frame.
Affected Products
FortiOS version 7.2.0 through 7.2.3
FortiOS version 7.0.0 through 7.0.9
FortiOS version 6.4.0 through 6.4.11
FortiOS version 6.2.0 through 6.2.12
FortiOS 6.0 all versions
FortiProxy version 7.2.0 through 7.2.2
FortiProxy version 7.0.0 through 7.0.8
FortiProxy version 2.0.0 through 2.0.12
FortiProxy 1.2 all versions
FortiProxy 1.1 all versionsEven when running a vulnerable FortiOS version, the hardware devices listed below are *only* impacted by the DoS part of the issue, *not* by the arbitrary code execution (non-listed devices are vulnerable to both):
FortiGateRugged-100C
FortiGate-100D
FortiGate-200C
FortiGate-200D
FortiGate-300C
FortiGate-3600A
FortiGate-5001FA2
FortiGate-5002FB2
FortiGate-60D
FortiGate-620B
FortiGate-621B
FortiGate-60D-POE
FortiWiFi-60D
FortiWiFi-60D-POE
FortiGate-300C-Gen2
FortiGate-300C-DC-Gen2
FortiGate-300C-LENC-Gen2
FortiWiFi-60D-3G4G-VZW
FortiGate-60DH
FortiWiFi-60DH
FortiGateRugged-60D
FortiGate-VM01-Hyper-V
FortiGate-VM01-KVM
FortiWiFi-60D-I
FortiGate-60D-Gen2
FortiWiFi-60D-J
FortiGate-60D-3G4G-VZW
FortiWifi-60D-Gen2
FortiWifi-60D-Gen2-J
FortiWiFi-60D-T
FortiGateRugged-90D
FortiWifi-60D-Gen2-U
FortiGate-50E
FortiWiFi-50E
FortiGate-51E
FortiWiFi-51E
FortiWiFi-50E-2R
FortiGate-52E
FortiGate-40F
FortiWiFi-40F
FortiGate-40F-3G4G
FortiWiFi-40F-3G4G
FortiGate-40F-3G4G-NA
FortiGate-40F-3G4G-EA
FortiGate-40F-3G4G-JP
FortiWiFi-40F-3G4G-NA
FortiWiFi-40F-3G4G-EA
FortiWiFi-40F-3G4G-JP
FortiGate-40F-Gen2
FortiWiFi-40F-Gen2Solutions
Please upgrade to FortiOS version 7.4.0 or above
Please upgrade to FortiOS version 7.2.4 or above
Please upgrade to FortiOS version 7.0.10 or above
Please upgrade to FortiOS version 6.4.12 or above
Please upgrade to FortiOS version 6.2.13 or above
Please upgrade to FortiProxy version 7.2.3 or above
Please upgrade to FortiProxy version 7.0.9 or above
Please upgrade to FortiOS-6K7K version 7.0.10 or above
Please upgrade to FortiOS-6K7K version 6.4.12 or above
Please upgrade to FortiOS-6K7K version 6.2.13 or aboveWorkaround for FortiOS:
Disable HTTP/HTTPS administrative interface
OR
Limit IP addresses that can reach the administrative interface:
config firewall address
edit "my_allowed_addresses"
set subnet <MY IP> <MY SUBNET>
end
Then create an Address Group:
config firewall addrgrp
edit "MGMT_IPs"
set member "my_allowed_addresses"
end
Create the Local in Policy to restrict access only to the predefined group on management interface (here: port1):
config firewall local-in-policy
edit 1
set intf port1
set srcaddr "MGMT_IPs"
set dstaddr "all"
set action accept
set service HTTPS HTTP
set schedule "always"
set status enable
next
edit 2
set intf "any"
set srcaddr "all"
set dstaddr "all"
set action deny
set service HTTPS HTTP
set schedule "always"
set status enable
end
If using non default ports, create appropriate service object for GUI administrative access:
config firewall service custom
edit GUI_HTTPS
set tcp-portrange <admin-sport>
next
edit GUI_HTTP
set tcp-portrange <admin-port>
end
Use these objects instead of "HTTPS HTTP "in the local-in policy 1 and 2 below.
When using an HA reserved management interface, the local in policy needs to be configured slightly differently - please see: https://community.fortinet.com/t5/FortiGate/Technical-Tip-How-to-configure-a-local-in-policy-on-a-HA/ta-p/222005
Please contact customer support for assistance.
Acknowledgement
Internally discovered and reported by Kai Ni from Burnaby InfoSec team. -
Access can be gained through CoH3 Steam Store page.
Schedule
Registration
- January 4th – January 13th
- Playtest registration can be found on the CoH3 Steam store page here.
Multiplayer Tech Test
- Wednesday, Jan 11th @ 10am PT to Monday, Jan 16th @ 10am PT
Planned Downtime
- January 12th from 1pm PT to 3pm PT
- Dependent on player numbers
Backup Downtime
- January 13th – 10am PT to 12pm PT
- We will only use this downtime if we did not conduct maintenance on January 12th
- Dependent on player numbers
Once the planned downtime is complete, we will be providing access to the Annihilation victory condition.
Review :
The game has been dumbed down a lot since Company of Heroes 1
Comparing to gameplay of CoH1 , This game look like a Console edition or even a Mobile edition
Textures of the units are so big and colored like it is a Fortnite of Heroes game , The tank shells and mortar shells , are so slow that you can even watch them travel.
Zoom level is so bad that you can't even focus on more than what you are looking at , a tank and an infantry unit and you will feel overwhelmed because you are almost sitting with the tank crewan
Coming from Blitzkrieg Mod from Company of Heroes 1 , this game feels so much downgraded , even more downgraded than what Company of Heroes 2 had.
In the positive side , the animation and soldiers and some of the sounds are good, but still need improvement , like for MG42 , it should rip anyone infront of it and also it have a unique sound , but in game it feels like it's a paintball MG42
Tanks repeadetly hitting soldiers with tank shells , mortar falling multiple times on soldiers units , but nothing happens to them only after the 5th or 6th round
-
You can find your own stats from the game here : https://quake-stats.bethesda.net
-

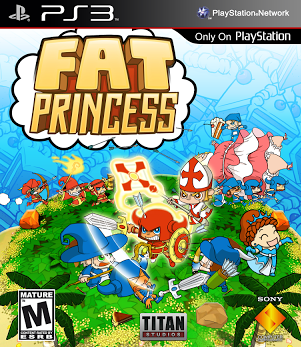
https://wiki.rpcs3.net/index.php?title=Fat_Princess
Download link -
Updated Link: https://www.mediafire.com/file/6smy7rfxnr6e2uv/Fat+Princess+PSN+[NPEA-00111].zip/fileRPCS3 Emulator :
Sadly this version of Fat Princess cannot be found anywhere and Sony removed it from the Store
For the memories we put it back.
-
Status_Breakpoint Fix
If you recently try to browse to WhatsApp Web for example and you would receive this error in your Google Chrome

In this version :
QuoteVersion 106.0.5249.119 (Official Build) (64-bit)
You have to change the TimeZone in Windows from International Date Line West -12:00 to your actual TimeZone.
Then this error should disappear.
Google should fix this in Chrome 107.
-
I actually hate ZOOM and hate ZOOM Meetings

-
8 hours ago, New_Style_xd said:
We explain how attackers can steal your credentials and how you can prevent it.

Spy Trojans.
phishing
Browser attacks
Public Wi-Fi
Passwords all over the place
external leaksMost common ways are Phishing with fake login websites , with people that won't really notice that it's not the original page
Or people who would run malware that would silently steal their stuff from their PC while they are unaware.
-
 1
1
-
-
On 9/1/2022 at 11:07 PM, New_Style_xd said:
Google will pay up to BRL 164,000 to anyone who discovers vulnerabilities
The company announced the launch of a bug bountry program that will pay researchers who identify vulnerabilities in software that is part of its open source projects.
Yes, Google and big companies will always put a prize for people who will report vulnerabilities so they would earn money from it , rather than selling it in darknet or some other places.
-
 1
1
-
-

Does anybody still play this game? , It's completely playable on RPCS3 with multiplayer support up to 4 people.
-
Wallpapers
in Art
You shall not pass!
 https://wall.alphacoders.com/big.php?i=1026646
https://wall.alphacoders.com/big.php?i=1026646
-
On 6/20/2022 at 7:09 PM, New_Style_xd said:
The threats hidden in malware on routers
Malware can infect your router, slow down your Internet connection, and steal data. We explain how to secure your Wi-Fi.You scan your computer every week, update systems and programs promptly, use strong passwords, and generally take care of yourself online… but for some reason, your internet is slow and some websites deny you access? It could be malware not on your computer, but on the router.
The router is the first layer of protection which is the Firewall which will protect and cover all the devices from WAN attacks , it is important to keep the router with an up-to-date firmware.
-
 1
1
-
-
On 6/8/2022 at 8:44 PM, New_Style_xd said:
Well, starting this topic, I'll tell you which one I use and why.
- I use vivaldi.
- And the chromium based browser.
- There is a privacy and ad blocking tool.
- Super Personalized with several themes and formats.
- Safe browser.
- Has email manager
- password manager
- Only using and testing will see how good this browser is.My personal choice would go to Firefox , more privacy forcused and open sourced browser , and then after that I would go for Chromium
-
 1
1
-
-
11 hours ago, New_Style_xd said:
Really, if it's used the good one is better used to clean up temporary files.
I used to clean Temp files and registry etc , but those days I just don't do
Windows will eventually do it by itself, unless I need to free up some disk space I start removing things.
-
 1
1
-
-
This has been fixed in Version 98.0.4758.80 (Official Build)
-
Recently with this update , there was a bug introduced that prevents users from dragging the tabs or moving them to another window , dragging the tab to another place would result in the tab opening a new window , it cannot be moved at all , a fix should be coming in version 98
But the workaround for it
Settings > Appearances > Turn off "Use system title bar and borders"
Link for settings : chrome://settings/appearance

Bug can be tracked through here : https://bugs.chromium.org/p/chromium/issues/detail?id=1279532
-
Download Windows 11
There are 3 options below for installing or creating Windows 11 media. Check out each one to determine the best option for you.
If you are upgrading from Windows 10, we recommend that you wait until you are notified through Windows Update that the upgrade is ready for your PC.
Before installing, please refer to the PC Health Check app to confirm your device meets the minimum system requirements for
Windows 11 and check the Windows release information status for known issues that may affect your device.https://www.microsoft.com/en-us/software-download/windows11
Installed on VMWARE Workstation - Machine must be encrypted , TPM must be added













Trojan Dropper Remcos - Removal and Cleaning
in Malware Infection Assistance
Posted
More info is found here about Remcos Loader
Guloader - https://any.run/malware-trends/guloader
And one more VBS file related to same Trojan https://www.virustotal.com/gui/file/eb1d835b72b54ec4d9553aefe22e30893df403ca128f826455972311e0493806/detection